Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Flipper Zero: Hardware Hacking JTAG and SWD Webcast
The Flipper Zero is known as a hacking multitool. It can cover a range of hacking from sub-ghz ...
Continue Reading
What are SQL Injection Vulnerability (SQLi), How to Identify Them, and How to Prevent
Recently, the FBI and CISA released a Secure by Design alert calling for the elimination of SQL ...
Continue Reading
Exploring Sentry Safe Exploit on the Flipper Zero with Logic Analyzer
hacking |
hardware |
flipper zero |
sentry |
safe |
logic analyzer
Overview I recently had a friend that wanted to learn how to use a logic analyzer. Given the number ...
Continue Reading
Flipper Zero: A Hardware Hacking Multitool Webcast
Training |
hacking |
hardware |
webcast |
flipper zero
The Flipper Zero is known as a hacking multitool. It can cover a range of hacking from sub-ghz ...
Continue Reading
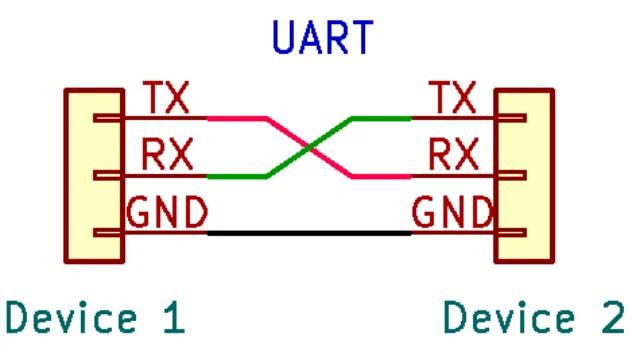
Hardware Hacking: Interfacing to UART with Your Computer
In my previous article, we covered identification and mapping of the UART interface. In that ...
Continue Reading
Hardware Hacking: Finding UART Pinouts on PCBs
In my previous article, we started to explore the Universal Asynchronous Receiver/Transmitter ...
Continue Reading
Hardware Hacking: Introduction to the UART Interface
I wanted to provide some information about hardware and firmware hacking in our blogs. To get the ...
Continue Reading
Introduction to Writing Nmap Scripting Engine (NSE) Scripts
NMAP |
programming |
NSE
One thing I notice a lot of people are missing in their skill set as security professionals is the ...
Continue Reading
How to Obfuscate Strings in Rust the Easy Way Using the litcrypt Crate
Overview Static strings in a binary can make the life easier for reverse engineers, be those ...
Continue Reading
Privilege Escalation via File Descriptors in Privileged Binaries
application security |
professionally evil |
Secure Ideas |
Linux |
programming |
File Descriptors |
SetUID |
Privilege Escalation
Today I wanted to cover an application security topic that applies to SetUID binaries. As we all ...
Continue Reading
Has contents: true
Total pages: 3
Current page: 0