Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
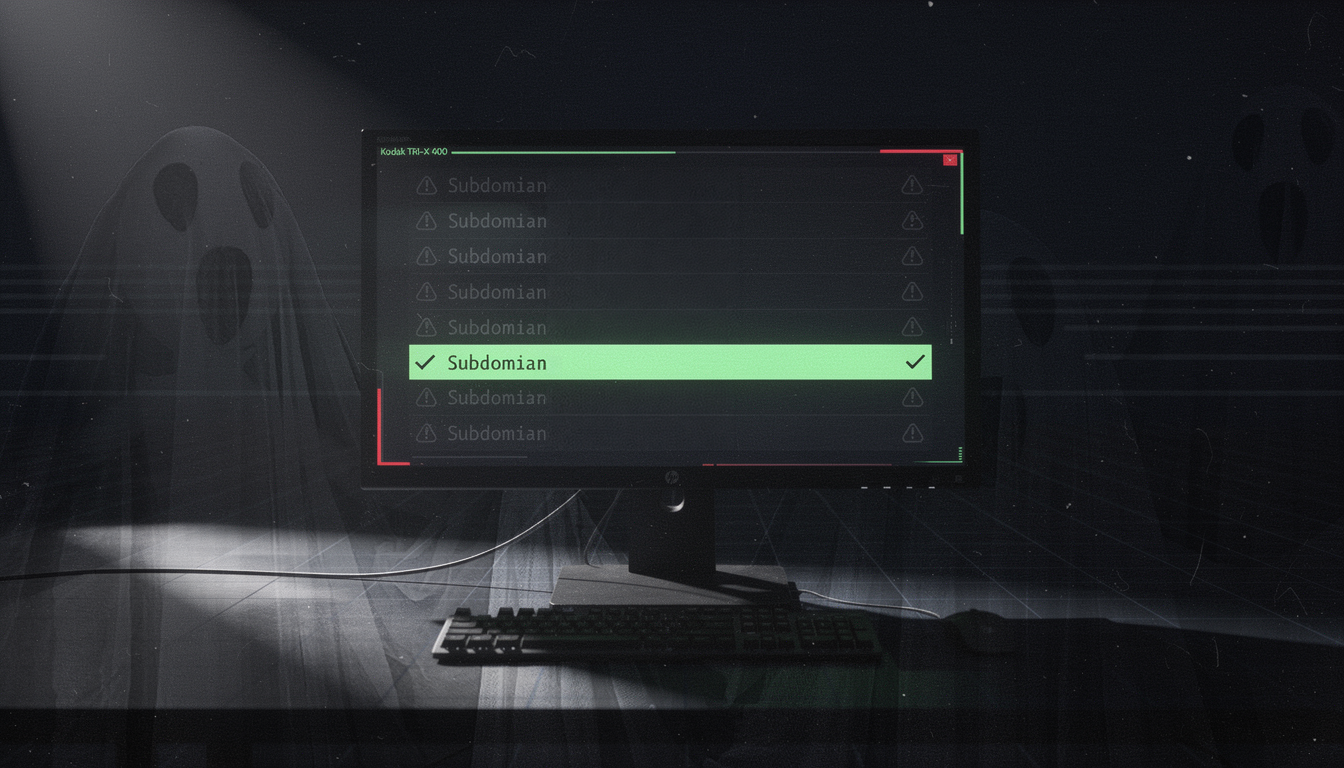
Detecting Dangling SaaS Subdomains and Real Subdomain Takeovers
Subdomain takeover is one of those vulnerabilities that refuses to die. Every few years it gets ...
Continue Reading
AI Agents: Clippy With Root Access
There’s a new kind of software showing up in your Slack, IDE, and cloud console and it’s AI agents. ...
Continue Reading
Evaluating AI Language Tutors Through a Security Lens
Evaluating AI Language Tutors Through a Security Lens Over the past year or so, I have seen a ...
Continue Reading
Rolling for Resilience Part 3: Battle Prep - The Scrolls of Response
This is the third post in this series addressing my perspective on the current state of ...
Continue Reading
Paths to Power in Active Directory Part 2: ESC1 – No One, Yet Anyone
This is the second post in this series. Part I can be found here.
Continue Reading
Extract Secrets from Multiple Configuration Files Using Vim
You're SSH'd into a compromised Linux server during a penetration test. You've found the ...
Continue Reading
Paths to Power in Active Directory Part 1: How AD CS Misconfigurations Become the Keys to the Kingdom
An Introduction to Active Directory Certificate Services (AD CS) I am still pretty new to ...
Continue Reading
No Broadcast Traffic? No Problem! - NetExec SMB Slinky Module
As pentesters, tools such as Responder and Ntlmrelayx are great tools for capturing hashes or ...
Continue Reading
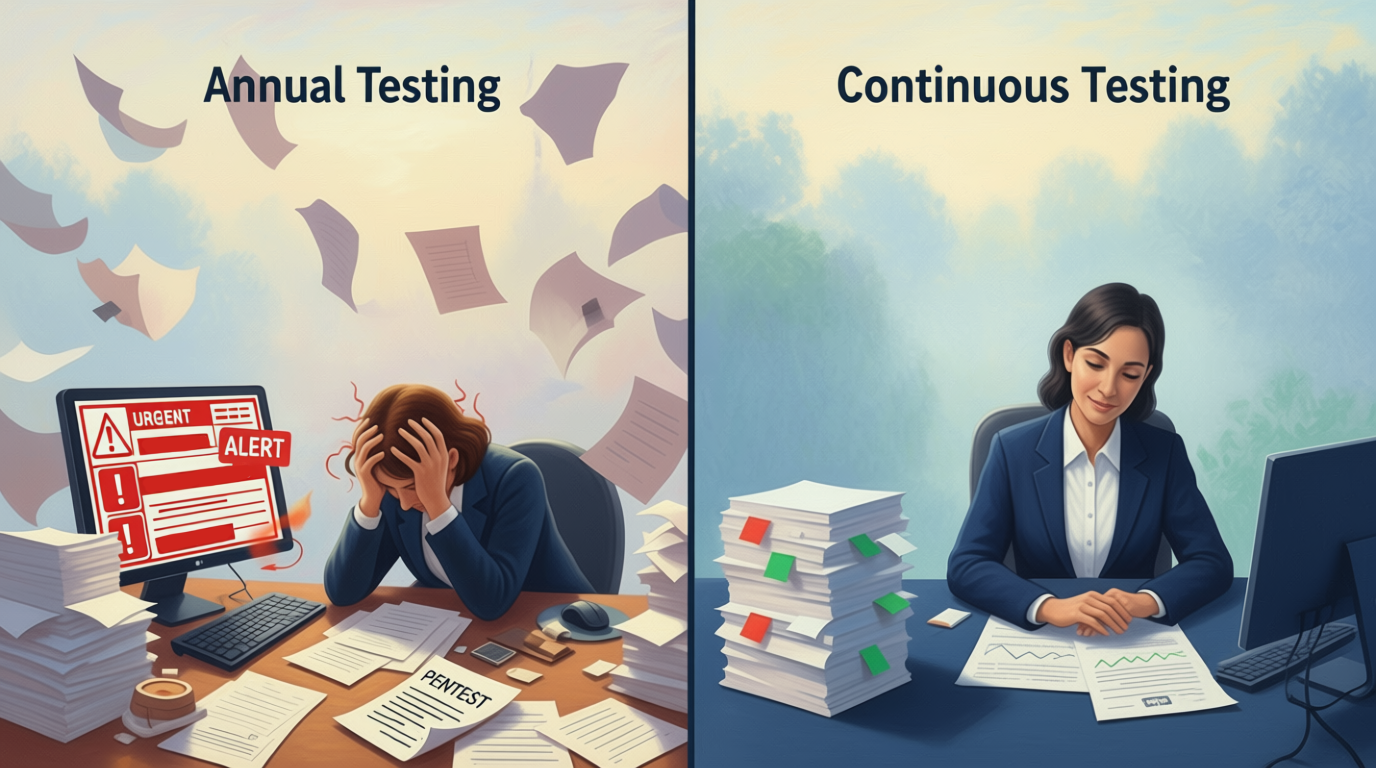
Annual Pentests Aren't Cutting It Anymore: Why Continuous Testing Beats Scrambling at Renewal Time
Let's be honest about something: if you're still relying on that once-a-year penetration test to ...
Continue Reading
Quantum Leaping Through Data: Preparing for the Quantum Encryption Transition
best practices |
compliance |
risk assessment |
NIST |
CISA
Quantum computing and its implications for cryptography isn't a new discussion. Security ...
Continue Reading
Your Risk Framework Is Broken: The Al Reality Check Every CISO Needs
Every risk management framework in cybersecurity relies on the same fundamental equation: Risk = ...
Continue Reading
Has contents: true
Total pages: 33
Current page: 2