Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Mobile Testing Considerations
penetration testing |
Secure Ideas |
cyber security |
mobile application security testing |
mobile app penetration testing |
mobile application development |
mobile application testing |
testing mobile applications |
iOS certificate pinning |
mobile application vulnerability assessment |
mobile application security assessment |
mobile app security analysis |
secure mobile application development practices |
android app security testing |
iOS app security testing |
android certificate pinning |
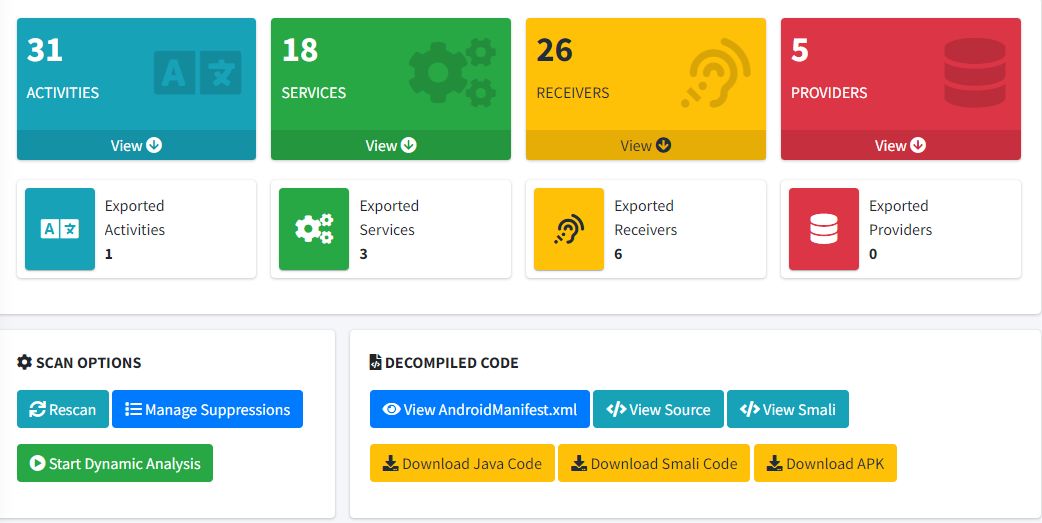
MobSF
Testing In Mobile Applications In today’s world, the significance of mobile applications in our ...
Continue Reading
The reason I stopped using Postman for API Pentests
I’ve been a proponent of Postman for a number of years. I’ve written and spoken about using it in ...
Continue Reading
Exploring Sentry Safe Exploit on the Flipper Zero with Logic Analyzer
hacking |
hardware |
flipper zero |
sentry |
safe |
logic analyzer
Overview I recently had a friend that wanted to learn how to use a logic analyzer. Given the number ...
Continue Reading
Webcast: Minor Flaws, Cumulative Risks
Imagine unraveling a classic whodunit murder mystery, where every subtle clue—a misplaced glove, a ...
Continue Reading
Mission Imfuzzable: How to Fuzz Web Apps you can't Intercept
Introduction Fuzzing is a critical technique for finding vulnerabilities in web applications by ...
Continue Reading
Webcast: Thrift Store Cracking Server: Popping Hashes Guide
(image was generated by Stable Diffusion, and is not an accurate representation of our cracking ...
Continue Reading
Taming the Enterprise AI Beast Webcast
As artificial intelligence (AI) continues to become more and more integral to business operations, ...
Continue Reading
12 Hacks of Christmas Day 12: Twelve Drummers Deleting Digital Clutter
🎵 On the twelfth day, clear digital clutter with twelve drummers deleting. Regularly review and ...
Continue Reading
12 Hacks of Christmas Day 11: Eleven Pipers Practicing Safe Browsing
🎵 On the eleventh day, practice safe browsing with eleven pipers practicing. Be mindful of the ...
Continue Reading
12 Hacks of Christmas Day 10: Ten Lords a-Cautious Shopping
🎵 On the tenth day, be cautious when shopping with ten lords a-cautious shopping. Stick to ...
Continue Reading
Has contents: true
Total pages: 40
Current page: 5