Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
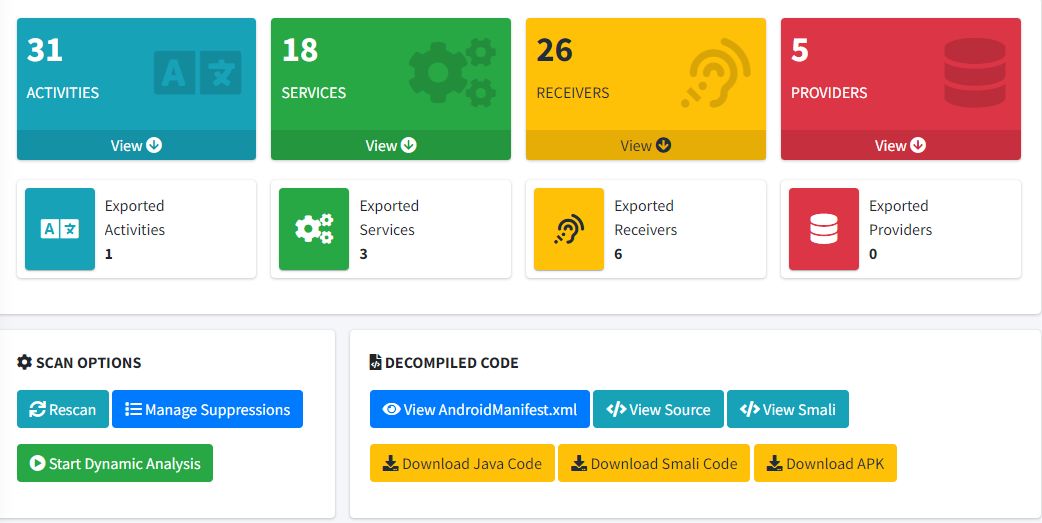
Mobile Testing Considerations
penetration testing |
Secure Ideas |
cyber security |
mobile application security testing |
mobile app penetration testing |
mobile application development |
mobile application testing |
testing mobile applications |
iOS certificate pinning |
mobile application vulnerability assessment |
mobile application security assessment |
mobile app security analysis |
secure mobile application development practices |
android app security testing |
iOS app security testing |
android certificate pinning |
MobSF
Testing In Mobile Applications In today’s world, the significance of mobile applications in our ...
Continue Reading
The reason I stopped using Postman for API Pentests
I’ve been a proponent of Postman for a number of years. I’ve written and spoken about using it in ...
Continue Reading
CyberScream - Hacking Like a Ghost(face)
consulting |
data breach |
penetration testing |
professionally evil |
hacking |
analysis |
cybersecurity |
pentesting |
phishing |
security breach |
exploits |
Halloween |
webcast
It’s that most hauntingly wonderful time of year again! Halloween is upon us, along with the dread ...
Continue Reading
Navigating Evolving Regulations: Staying Ahead of Change
In today's rapidly expanding business world, the only constant seems to be change itself. One of ...
Continue Reading
Understanding Server-Side Template Injection (SSTI)
Testing |
Training |
QA |
web penetration testing |
penetration testing |
application security |
OWASP |
web application security |
methodology |
OWASP Top 10
Web applications play a vital role in delivering dynamic content to users. To achieve this, ...
Continue Reading
Introducing BILE - Groundbreaking Classification for Web App
Training |
penetration testing |
OWASP |
web application security |
BILE |
OWASP Top 10 |
BILE Classification Scheme |
vulnerability classification
As a seasoned web application penetration tester, I've always felt that there should be a more ...
Continue Reading
Introducing PETaaS®: Professionally Evil Testing as a Service
We're thrilled to announce the launch of our latest offering: Professionally Evil Testing as a ...
Continue Reading
Twelve Days of ZAPmas - Day 2 - The Edge of Tomorrow
Day 2 - The Edge of Tomorrow - Replaying and Tampering with Requests Fuzzing and tampering are like ...
Continue Reading
What are the key requirements of the GLBA Safeguards Rule?
information security |
penetration testing |
CISSP |
education |
compliance |
risk assessment |
security controls |
information security program |
GLBA |
Safeguards Rule |
Dec 9, 2022 |
automotive |
banking |
vulnerability assessment
The Gramm-Leach-Bliley Act (GLBA) contains the Safeguards Rule. This requires financial businesses ...
Continue Reading
Application Security 202: Vulnerabilities Accepted
Testing |
Vulnerability |
Guidance |
data breach |
information security |
penetration testing |
application security |
professionally evil |
Secure Ideas |
hacking |
best practices |
cybersecurity |
Privilege Escalation
vul·ner·a·bil·i·ty The quality or state of being exposed to the possibility of being attacked or ...
Continue Reading
How to allow multiple RDP sessions
Training |
penetration testing |
pentesting |
Windows |
technology tips and tricks |
rdp |
sysadmin |
system administration
The goal of this article is to walk through how to set up a Windows host to allow multiple remote ...
Continue Reading
Has contents: true
Total pages: 2
Current page: 0