Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Quick Bites Episode 11 – Ranking Application Risks
application security |
hacking |
pentesting |
Quick Bites |
risk assessment |
appsec |
application risk |
ranking risk
Threats often evolve faster than defenders can figure out how to prevent them. That’s why keeping up with the threats and assessing the risk associated with them is so important. Here at Secure Ideas, we believe that assessing and ranking application risks is key. In this Quick Bites, we’ll talk ...
Continue Reading
Never miss a Professionally Evil update!
Quick Bites Episode 10 – Half Shells and Full Shells
hacking |
pentesting |
shell |
Quick Bites |
reverse shells |
terminal |
python |
python3 |
netcat |
command line |
nc
I wanted to share a really cool technique that I found out about recently. Now I will say this is ...
Continue Reading
The reason I stopped using Postman for API Pentests
I’ve been a proponent of Postman for a number of years. I’ve written and spoken about using it in ...
Continue Reading
Using PETaaS to Lower Your Cyber Insurance Costs
Modern networks have more than their fair share of risks, with the most damaging often being data ...
Continue Reading
CyberScream - Hacking Like a Ghost(face)
consulting |
data breach |
penetration testing |
professionally evil |
hacking |
analysis |
cybersecurity |
pentesting |
phishing |
security breach |
exploits |
Halloween |
webcast
It’s that most hauntingly wonderful time of year again! Halloween is upon us, along with the dread ...
Continue Reading
Twelve Days of ZAPmas - Day 2 - The Edge of Tomorrow
Day 2 - The Edge of Tomorrow - Replaying and Tampering with Requests Fuzzing and tampering are like ...
Continue Reading
How to allow multiple RDP sessions
Training |
penetration testing |
pentesting |
Windows |
technology tips and tricks |
rdp |
sysadmin |
system administration
The goal of this article is to walk through how to set up a Windows host to allow multiple remote ...
Continue Reading
Wild West Hackin Fest 2022: The Return
Training |
security |
samuraiWTF |
web penetration testing |
information security |
security awareness |
application security |
professionally evil |
Secure Ideas |
hacking |
cybersecurity |
pentesting |
web application security |
technology |
security conference
Man, San Diego is beautiful. I don't know exactly why John Strand and Black Hills Information ...
Continue Reading
How to Create Custom Probes For NMAP Service/Version Detection
network |
hacking |
cybersecurity |
pentesting |
scanning |
NMAP |
version |
service |
probe |
ports |
match |
chrome |
debugging |
nmap-service-probes |
softmatch |
rarity |
directive |
remote
Overview NMAP is a fantastic tool for performing initial reconnaissance and enumeration. A simple ...
Continue Reading
Computers are People Too
There are those rare times during pen tests, when you are on a client’s network and you don’t have ...
Continue Reading
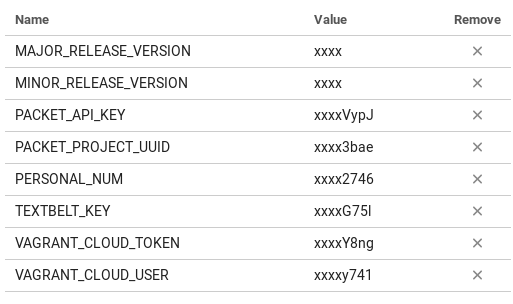
Automating Red Team Homelabs: Part 2 – Build, Pentest, Destroy, and Repeat
pentesting |
automation |
API |
dev ops |
home lab
As of 2019-05-14 the Funny Stories section has been updated. Now that we understand what the goal ...
Continue Reading
A Container Hacker’s Guide to Living Off of the Land
hacking |
container hacking |
container security |
containerization |
pentesting |
living off the land
Sometimes as a pentester you find yourself in tricky situations. Depending on the type of ...
Continue Reading
Has contents: true
Total pages: 1
Current page: 1